
ESET Security
ESET’s award-winning security products are lightweight, fast and built with ConnectWise MSPs in mind.

ESET’s award-winning security products are lightweight, fast and built with ConnectWise MSPs in mind.
This solution is available for purchase directly from ConnectWise via the ConnectWise Marketplace and the ConnectWise sales team.
About ESET
For more than 30 years, ESET® has developed industry-leading IT security software and services, delivering instant, proactive protection against evolving cybersecurity threats for businesses worldwide. ESET’s award-winning security products are lightweight, fast and built with ConnectWise MSPs in mind.
ESET cybersecurity solutions are available for purchase through the ConnectWise Marketplace.
Review the ordering tab for more info, or click the pink “Buy Now” button to review purchasing options.
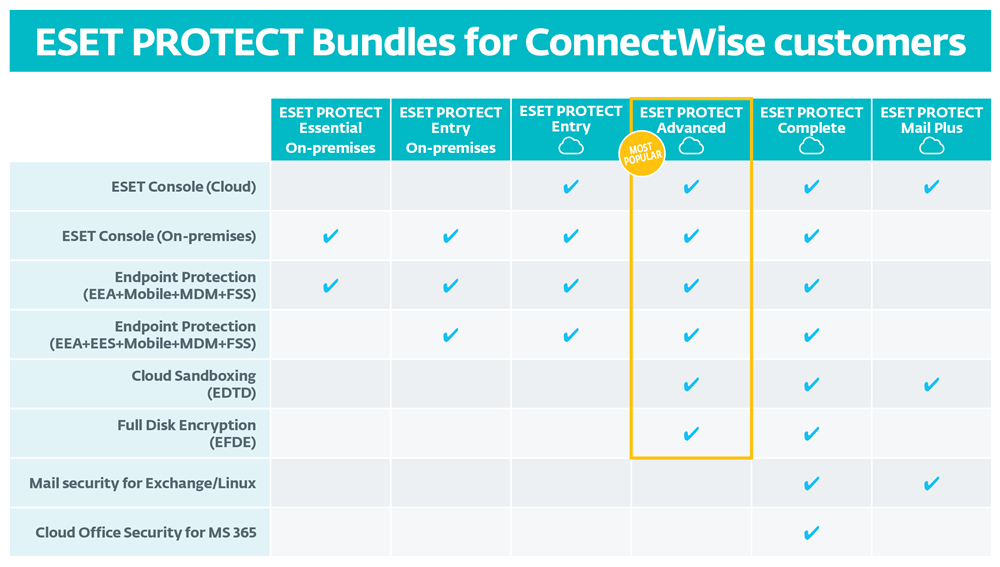
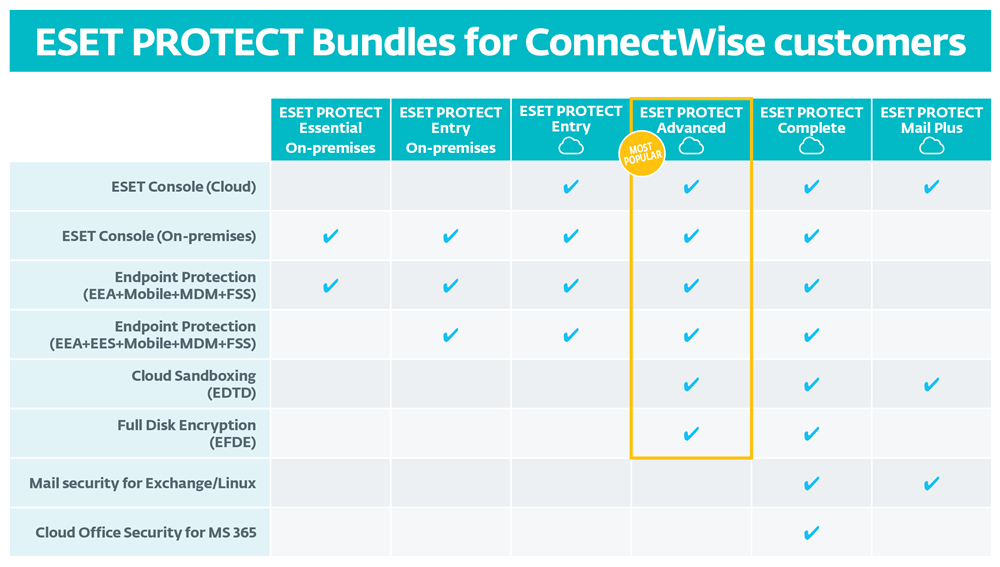
Be sure to check out the new ESET PROTECT Cloud bundle!
Complimentary ESET Deployment and Upgrade Service
Let our ESET experts guide you through your initial deployment or upgrade to the latest version. This white glove service is at no cost for ConnectWise customers with an active ESET business license. Schedule your deployment today!
Requirements: ESET Remote Administrator 6.2+
Features:
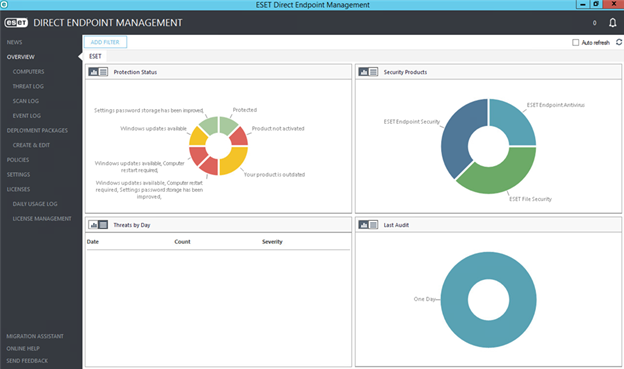
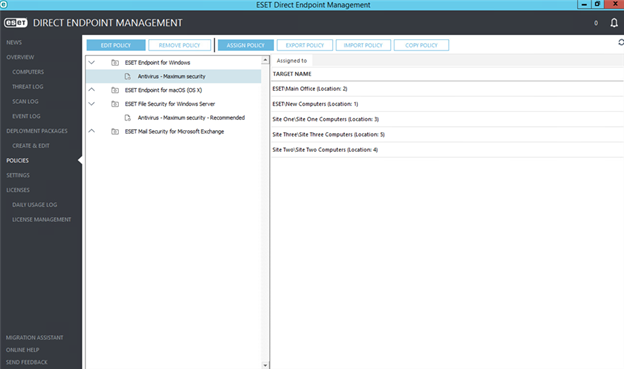
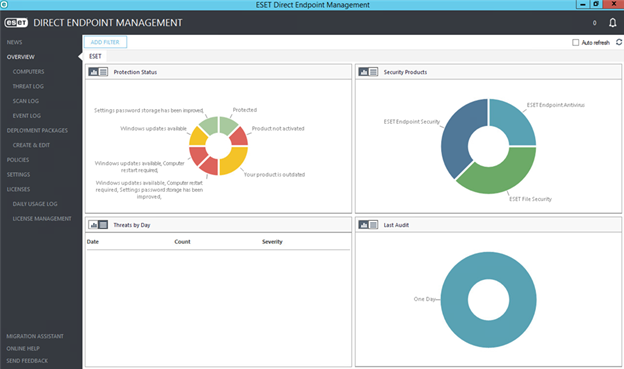
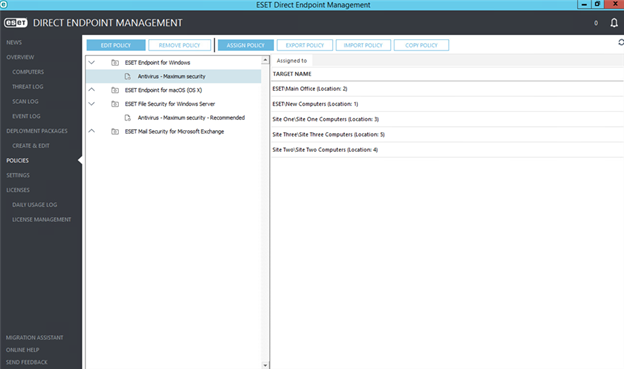
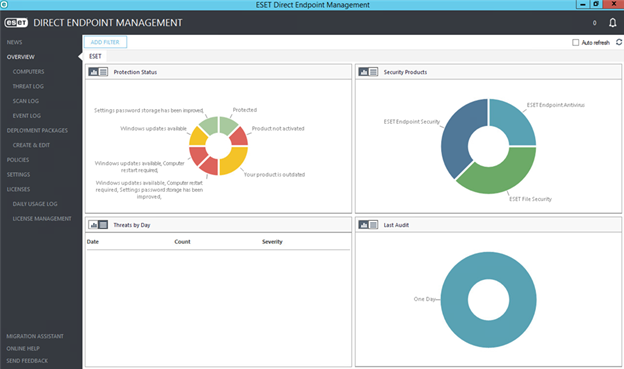
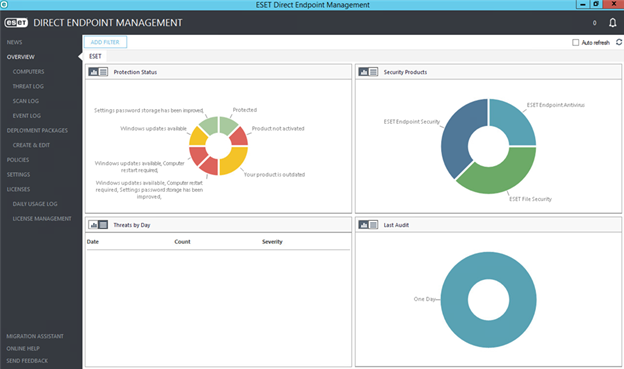
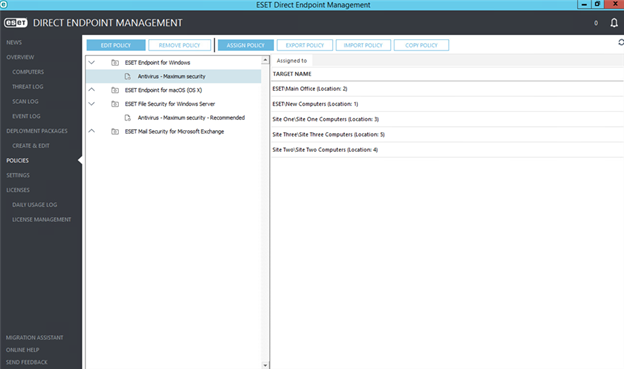
Requirements: Directly connect endpoints to ConnectWise Automate with no additional hardware, servers or intermediary software. By default, the ESET DEM plugin deploys the latest ESET endpoint product versions.
System requirements:
NOTE: The ESET DEM plugin for ConnectWise Automate is not compatible with computers managed by ESET Endpoint Encryption Enterprise Server.
Operating systems:
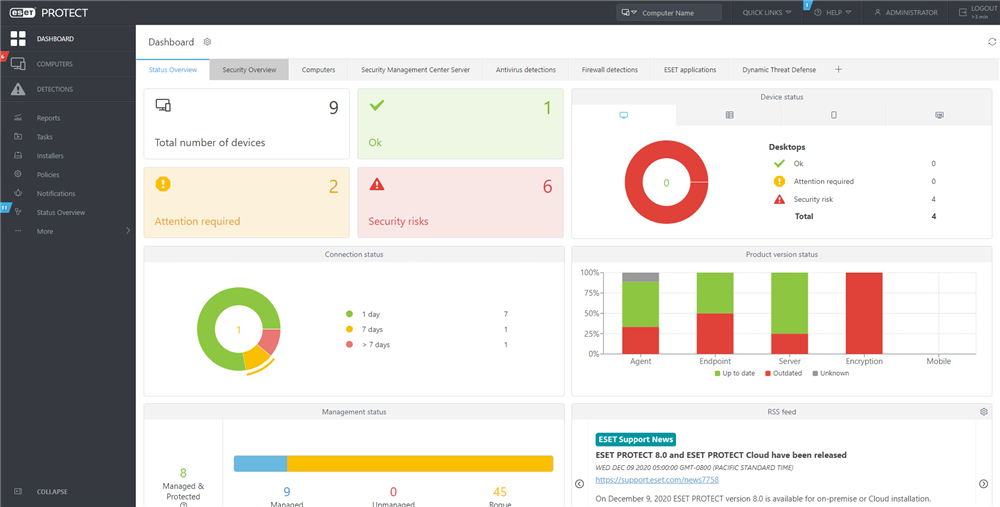
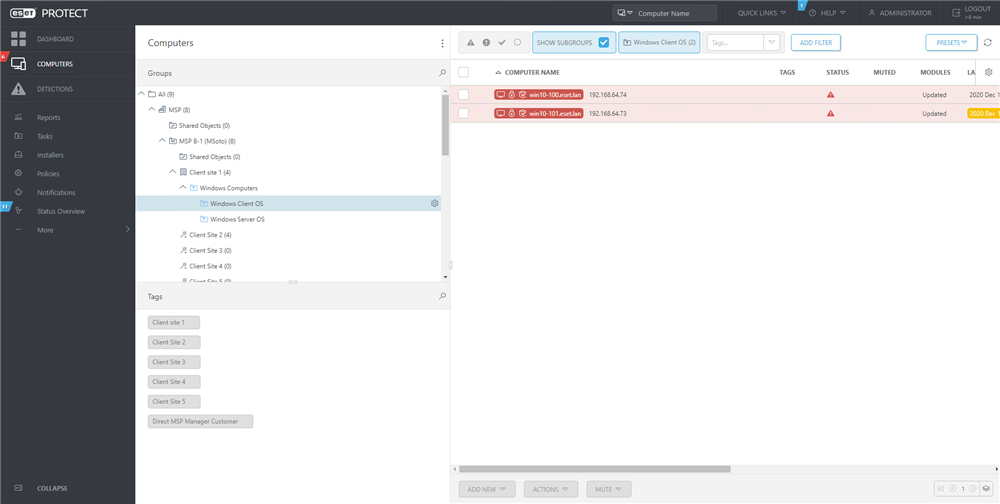
ESET Security Management Center (on-premise):
Single-pane of glass management of ESET Endpoints with advanced management and reporting options. Connect endpoints to ConnectWise Automate via ESET Remote Administrator plugins.
To use the ESET Remote Administrator Plug-in for ConnectWise, your system should meet or exceed the following requirements:
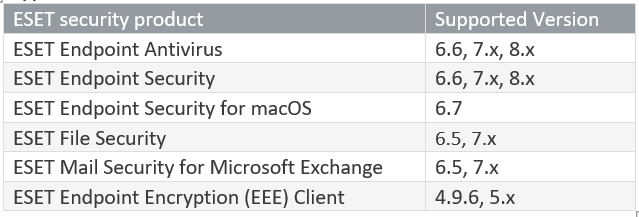
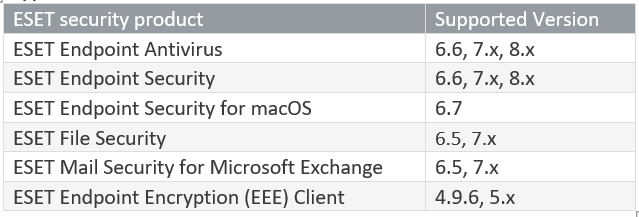
Supported ESET Products:
For detailed provisioning and purchasing documentation, please click here.
Provision your NEW ACCOUNT or migrate your existing ConnectWise Agreement to usage-based billing by clicking the BUY NOW button.
ESET Endpoint products are priced per device in most cases, with the exception of ESET Mail Security (per mailbox), Two-Factor Authentication and Cloud Office Security (per user), with monthly usage billed in arrears. Pricing is subject to change at any time. ESET is a third-party product sold and distributed by ConnectWise. The ConnectWise Privacy Policy is not applicable to the use of this third-party product.
Complimentary ESET Deployment and Upgrade Service
Let our ESET experts guide you through your initial deployment or upgrade to the latest version. This white glove service is at no cost for ConnectWise customers with an active ESET business license. Schedule your deployment today!
For product or procurement questions please contact Marketplace@ConnectWise.com
For ESET related technical support questions or issues please contact ESET directly for assistance. You may choose the route that suits you best and their team looks forward to serving you!
For ConnectWise application issues, please contact Help@ConnectWise.com.
About ESET
For more than 30 years, ESET® has developed industry-leading IT security software and services, delivering instant, proactive protection against evolving cybersecurity threats for businesses worldwide. ESET’s award-winning security products are lightweight, fast and built with ConnectWise MSPs in mind.
ESET cybersecurity solutions are available for purchase through the ConnectWise Marketplace.
Review the ordering tab for more info, or click the pink “Buy Now” button to review purchasing options.
Be sure to check out the new ESET PROTECT Cloud bundle!
Complimentary ESET Deployment and Upgrade Service
Let our ESET experts guide you through your initial deployment or upgrade to the latest version. This white glove service is at no cost for ConnectWise customers with an active ESET business license. Schedule your deployment today!
Requirements: ESET Remote Administrator 6.2+
Features:
Requirements: Directly connect endpoints to ConnectWise Automate with no additional hardware, servers or intermediary software. By default, the ESET DEM plugin deploys the latest ESET endpoint product versions.
System requirements:
NOTE: The ESET DEM plugin for ConnectWise Automate is not compatible with computers managed by ESET Endpoint Encryption Enterprise Server.
Operating systems:
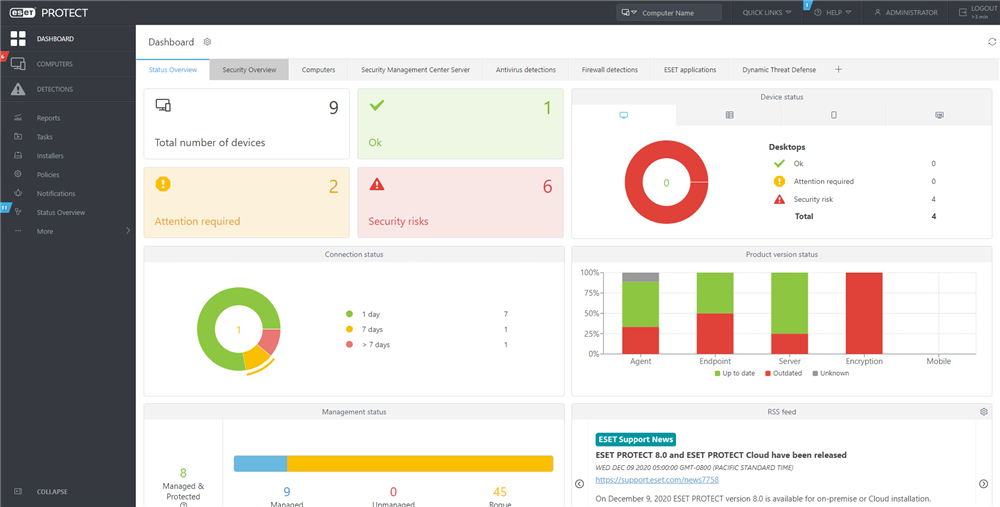
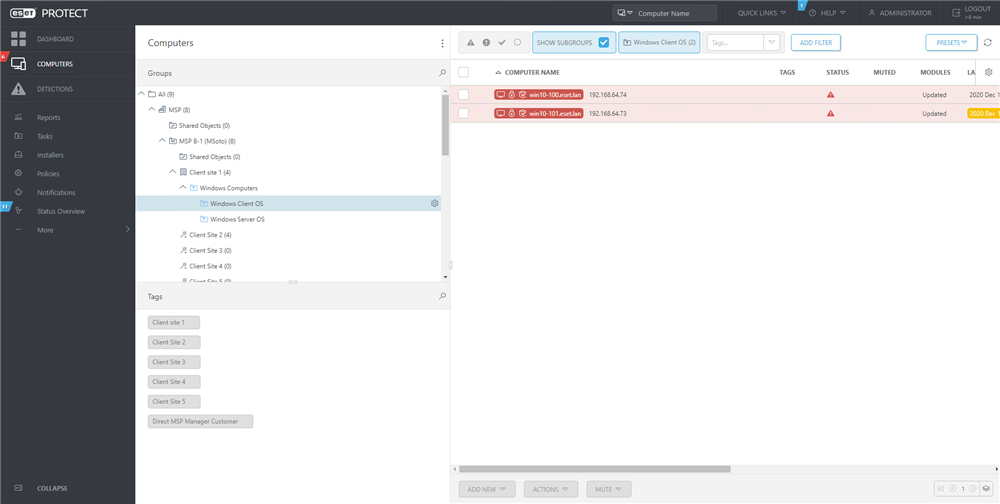
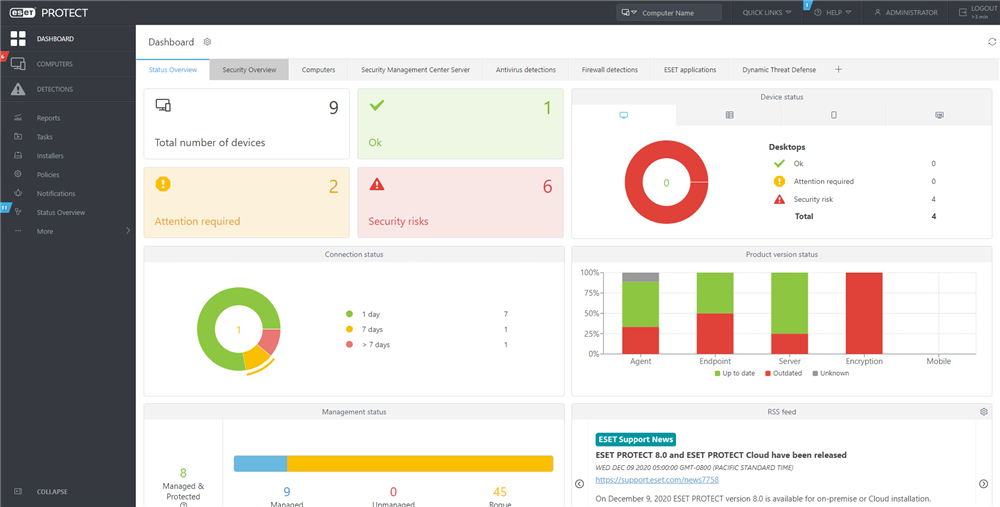
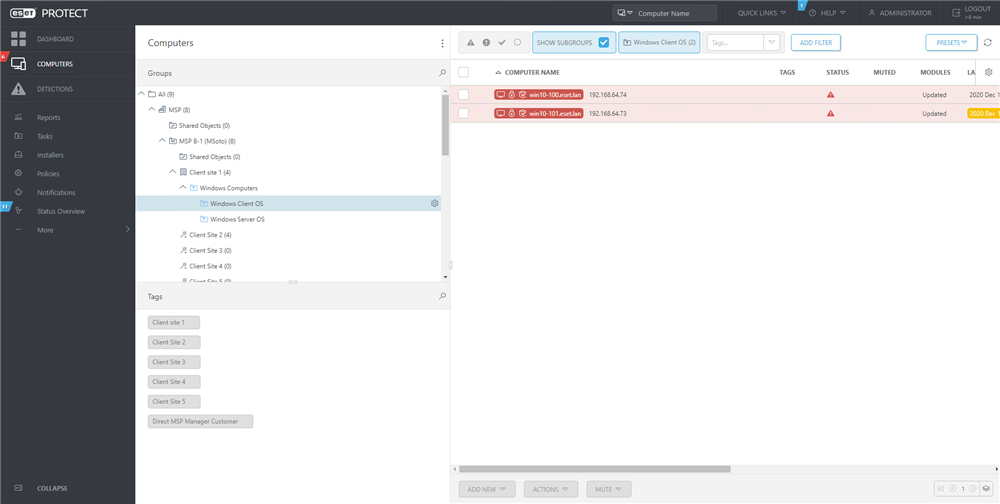
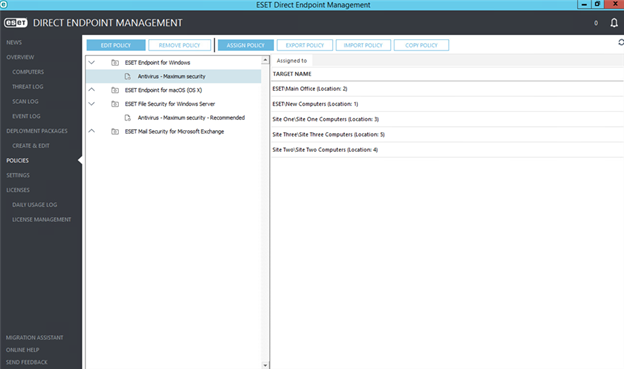
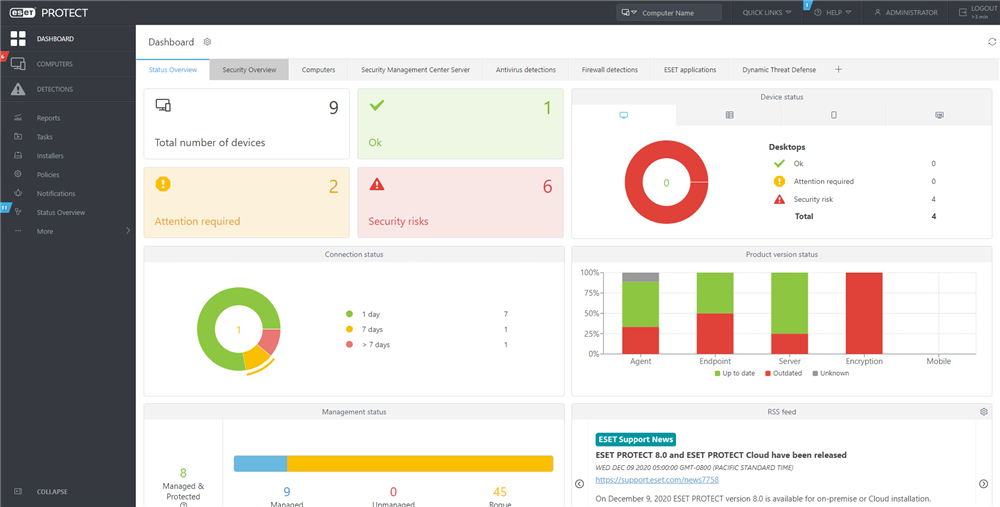
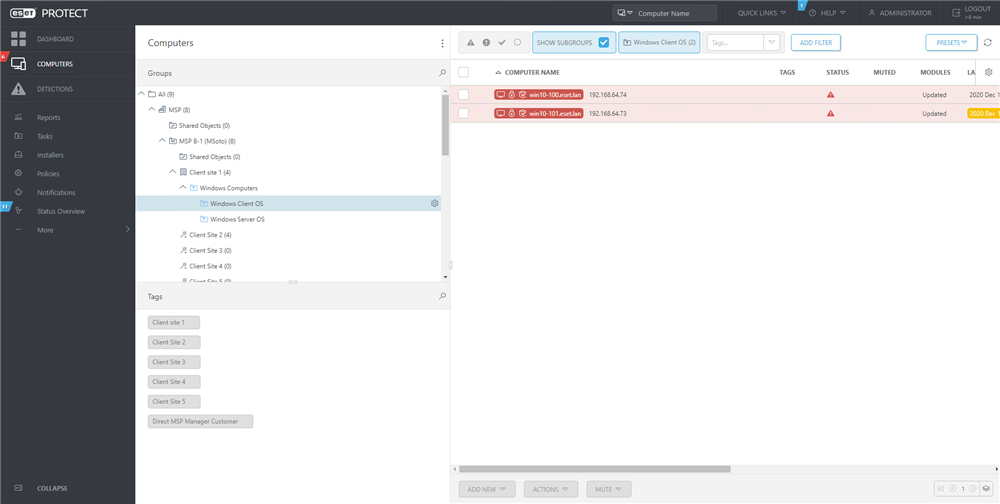
ESET Security Management Center (on-premise):
Single-pane of glass management of ESET Endpoints with advanced management and reporting options. Connect endpoints to ConnectWise Automate via ESET Remote Administrator plugins.
To use the ESET Remote Administrator Plug-in for ConnectWise, your system should meet or exceed the following requirements:
Supported ESET Products:
For detailed provisioning and purchasing documentation, please click here.
Provision your NEW ACCOUNT or migrate your existing ConnectWise Agreement to usage-based billing by clicking the BUY NOW button.
ESET Endpoint products are priced per device in most cases, with the exception of ESET Mail Security (per mailbox), Two-Factor Authentication and Cloud Office Security (per user), with monthly usage billed in arrears. Pricing is subject to change at any time. ESET is a third-party product sold and distributed by ConnectWise. The ConnectWise Privacy Policy is not applicable to the use of this third-party product.
Complimentary ESET Deployment and Upgrade Service
Let our ESET experts guide you through your initial deployment or upgrade to the latest version. This white glove service is at no cost for ConnectWise customers with an active ESET business license. Schedule your deployment today!
For product or procurement questions please contact Marketplace@ConnectWise.com
For ESET related technical support questions or issues please contact ESET directly for assistance. You may choose the route that suits you best and their team looks forward to serving you!
For ConnectWise application issues, please contact Help@ConnectWise.com.